Technology
Cloud Gaming: Video Game Playing On The Go

Cloud Gaming, sometimes also called internet gaming, is a kind of online gaming that functions on remote servers which are then connected to the user’s computer through the web browser. The server may be a third party website, such as a gaming website owned by Amazon or Yahoo, or it may be a specialized game server developed by an individual or group of individuals.
Some cloud servers are partially managed by their owners, while others are run by dedicated gaming platforms. The latter are popularly used by large online role-playing games (RPGs) such as World of Warcraft or Warhammer Online.
Cloud Gaming is similar to using a computer in a shared environment, except the user does not need to have his own hardware. Instead, he just needs a high quality internet connection, a computer that has enough memory to run the required software and a device capable of rendering graphics.
This is because most modern computers have built-in support for streaming. Some of the required components needed to run streaming games include a host system, a video card or graphics processing unit, a frame buffering server, a network adapter, and a router. In a typical cloud gaming setup, a client computer also needs a microphone, a camera, or a headset.
There are several advantages in using a cloud game streaming service. For example, they provide a stable, consistent high-end internet connection. Since it is controlled from a remote location, there is no problem with connectivity latency or reliability. Latency refers to delays that occur between the request from the remote server and the response from the client computer. When the connection is slow, the game can be delayed by several minutes, which can greatly affect the amount of fun a player gets from it.

Most cloud gaming services use streaming technologies that are capable of eliminating any kind of latency. This is important for casual gamers who want to play without having to deal with annoying lag. Even when the connection speed is slow, latency is eliminated, making the experience of playing even more enjoyable. The result is that people playing in this type of environment can expect to have an enjoyable gaming experience.
Another advantage to using cloud computing technology is that people can play the same video games over again. With the use of streaming technology, people can play their favorite games repeatedly without having to re-download the whole thing. As long as they have an internet connection, they can start right where they left off. The only requirement is that they have a modern PC or a gaming laptop that has sufficient processing power and memory to take advantage of the numerous streaming options available.
The last major advantage to using a streaming service for playing online games is security. With the use of a remote server, data is stored on servers that are secure. Therefore, there is no worry about private data being compromised because the information is stored on a secure location.
With this security feature, people can enjoy playing their games without worrying about the privacy of their personal data. Most cloud gaming services also offer round the clock customer support, so that gamers can get any assistance they need during gameplay.
Although most people agree that it is fun to play games with others around the world, they don’t always want to be limited by geography. To solve this problem, some of the better cloud gaming services have introduced consoles. A console is basically a computer that can be connected to the web. By signing up, players can play games from anywhere that has a modern Internet connection. The main drawback to playing through a console is that most gamers are used to playing with a keyboard and mouse, and without the additional input of a controller.
Summary
In summary, there are several advantages to using cloud gaming services to play video games. The main benefit is that there is no longer any risk of input lag or connection issues. In addition, most video game consoles are now cheaper than ever, and gamers no longer need to buy new gaming PCs. Lastly, most cloud gaming services include extra benefits such as round the clock customer support and other features that add convenience.
In summary, the introduction of consoles has reduced the need for many gamers to own multiple gaming PCs. If you enjoy playing first-person shooters, role-playing games, or even MMORPGs, you may want to check out the advantages provided by cloud computing.
Also Read: 5 Best Cloud Gaming Services in India 2020
Technology
Peering Through the Apple Vision Pro: A New Perspective on Smart Glasses

Discover the Future of Sight: Apple Vision Pro Unveils a Revolutionary Leap in Smart Glasses Technology and Augmented Reality Wearables.
Peering through the lens of the Apple Vision Pro, one is transported into a realm where smart glasses technology merges seamlessly with everyday life, offering a glimpse into the future of augmented reality wearables. This review will explore the intricate weave of innovation that Apple has spun into its smart eyewear, providing an insightful analysis of how these AR glasses stand to redefine our interaction with the digital world. As we explore the features, design, and user experience of the Apple Vision Pro, we invite you to join us in discovering how this cutting-edge technology could alter the fabric of our technological interactions and open up new vistas of possibility.
Table of Contents
- Unveiling the Apple Vision Pro: A Comprehensive Review
- The Evolution of Smart Glasses Technology: Where Does Apple Stand?
- Navigating the World with Augmented Reality Wearables: The Apple Vision Pro Experience
- Apple Smart Eyewear: Blending Style with Cutting-Edge Functionality
- Innovations in AR Glasses: How the Apple Vision Pro is Redefining the Genre
- How does the Apple Vision Pro enhance everyday experiences with augmented reality wearables?
- What are the standout features of the Apple Smart Eyewear in comparison to other smart glasses on the market?
- Can the Apple Vision Pro smart glasses technology replace traditional devices like smartphones or tablets?
- How has innovations in AR glasses been pushed forward by the release of Apple Vision Pro?
- What do reviews generally say about the user experience of the Apple Vision Pro?
- Conclusion
Unveiling the Apple Vision Pro: A Comprehensive Review
The Apple Vision Pro emerges as a beacon of innovation in the burgeoning field of smart glasses technology. Its sleek design belies the powerful technology housed within its frames. The high-resolution displays integrated into each lens offer users a crisp and vibrant view of their augmented world, with minimal intrusion into their field of vision. The responsive touchpad located on the side arms allows for intuitive control, ensuring that users can navigate through menus and applications with ease.Audio innovation is another standout feature, with spatial audio capabilities that create an immersive sound experience without the need for earphones. This not only enhances privacy but also maintains a connection with the environment. The Apple Vision Pro’s voice control is underpinned by Siri, which has been refined to understand context and nuance better than ever before.Battery life is a common concern with wearable technology, but the Apple Vision Pro addresses this with an all-day battery that supports wireless charging. This commitment to longevity ensures that users can rely on their smart glasses throughout their daily activities without fear of losing connection to their digital lives.
The Evolution of Smart Glasses Technology: Where Does Apple Stand?
Apple’s foray into smart glasses technology did not happen in isolation. The sector has seen various iterations and improvements over the years, with numerous companies attempting to strike a balance between functionality and wearability. However, where Apple stands out is in its dedication to refining these aspects to near perfection.The Apple Vision Pro builds upon lessons learned from earlier attempts by competitors, integrating advanced AR capabilities while maintaining a form factor that is both comfortable and stylish. This evolution is marked by Apple’s use of custom chipsets that optimise performance while conserving power, a critical factor in wearable tech.Moreover, Apple’s robust ecosystem allows for seamless integration with other devices, enhancing the utility of the Vision Pro. Whether it’s picking up a call from your iPhone or receiving turn-by-turn navigation from Maps, the interoperability is smooth and intuitive. This synergy between devices is not just convenient; it’s transformative, allowing users to stay connected in ways previously unimagined.
Navigating through your day-to-day life with the Apple Vision Pro offers an unparalleled experience. Augmented reality overlays digital information onto the physical world, and with the Vision Pro, this technology reaches new heights of clarity and relevance. Imagine walking down the street and seeing directional arrows on the pavement, guiding you to your destination, or looking at a restaurant and instantly viewing its menu and ratings.The potential for professional use is equally impressive. Architects could visualise buildings within a real-world context, while surgeons could have vital statistics and imaging displayed right before their eyes during procedures. The applications are as varied as they are groundbreaking.Privacy concerns are paramount when it comes to AR wearables, and Apple addresses this by implementing sophisticated data protection measures. Users can trust that their information is secure and that they have control over what they share and when.
Apple Smart Eyewear: Blending Style with Cutting-Edge Functionality
Apple has always placed a premium on design, and the Vision Pro smart eyewear is no exception. These glasses don’t just serve as a portal to augmented reality; they’re also a fashion statement. Available in various styles and finishes, they can complement any look, from business casual to evening chic.The materials used are lightweight yet durable, ensuring comfort during extended wear while also standing up to the rigours of daily use. The attention to detail extends to the lenses themselves, which are treated to be scratch-resistant and anti-reflective.But style does not come at the expense of functionality. Each pair is equipped with advanced sensors that detect gestures and eye movements, allowing users to interact with their device in a way that feels natural and unobtrusive. This harmony between form and function sets a new standard for what smart eyewear can be.
Innovations in AR Glasses: How the Apple Vision Pro is Redefining the Genre
The innovations present in the Apple Vision Pro mark a significant leap forward for AR glasses. One of the most notable advancements is in the realm of personalised experiences. The Vision Pro uses machine learning to understand user preferences and habits, tailoring notifications and content to suit individual needs.The environmental awareness of the device is another groundbreaking feature. Using LiDAR technology, the glasses can map surroundings in real-time, allowing for more accurate and responsive AR interactions. This not only improves user experience but also opens up new possibilities for app developers to create rich, immersive applications that interact with the world around us.Lastly, health monitoring capabilities have been subtly integrated into the design. The Vision Pro can track metrics such as heart rate and steps taken, encouraging users to stay active and mindful of their wellness. These health features blend seamlessly into the overall experience, reinforcing Apple’s commitment to enhancing lives through technology.
How does the Apple Vision Pro enhance everyday experiences with augmented reality wearables?
The Apple Vision Pro smart glasses are designed to seamlessly integrate augmented reality into daily life. By projecting information directly into the user’s field of vision these glasses allow for real-time interaction with notifications navigation and multimedia content without the need to look away from what you’re doing. Imagine walking down the street and getting turn-by-turn directions overlaid onto the real world or viewing a recipe right in front of your eyes while cooking. The hands-free convenience and immersive experience offered by the Apple Vision Pro make it a significant step forward in augmented reality wearables.
What are the standout features of the Apple Smart Eyewear in comparison to other smart glasses on the market?
Apple’s foray into smart eyewear with the Vision Pro brings several standout features that set it apart from competitors. One of the most talked-about features is its advanced retina display which offers crisp and vibrant visuals without being intrusive. Additionally the integration with Apple’s ecosystem allows for a seamless connection with other Apple devices enhancing functionality and user experience. The glasses also boast a sleek design that aligns with Apple’s aesthetic making them not only technologically advanced but also fashion-forward. Battery life and privacy features are also areas where the Apple Vision Pro outshines others offering users peace of mind and extended use throughout their day.
Can the Apple Vision Pro smart glasses technology replace traditional devices like smartphones or tablets?
While the Apple Vision Pro smart glasses offer an array of functionalities that overlap with smartphones and tablets they are not intended to replace these devices completely. Instead they complement them by providing an alternative way to access information and perform certain tasks. For instance while you might still prefer to watch a movie on your tablet’s larger screen the Vision Pro can provide quick glances at messages or emails without having to pull out your phone. They’re particularly useful for situations where using your hands or looking down at a screen is inconvenient or unsafe such as when you’re cycling or carrying groceries.
How has innovations in AR glasses been pushed forward by the release of Apple Vision Pro?
The release of the Apple Vision Pro has undoubtedly accelerated innovation in the AR glasses sector. Apple’s reputation for high-quality user-friendly products means that their entry into this market has raised expectations for what smart glasses can do. The Vision Pro’s sophisticated design and functionality have encouraged competitors to push the boundaries of their own AR technology. Moreover developers are now more incentivised to create apps and experiences tailored to AR wearables knowing there’s a high-quality platform available that can support more complex and engaging augmented reality experiences.
What do reviews generally say about the user experience of the Apple Vision Pro?
Reviews of the Apple Vision Pro have been largely positive with many users praising its intuitive interface and ease of use. Critics have highlighted how the glasses feel natural to wear with notifications and information appearing unobtrusively in the wearer’s line of sight. The device’s lightweight design has also received commendations making it comfortable for extended wear. Users have expressed appreciation for the customisation options available allowing them to tailor their experience to their preferences and needs. While there is always room for improvement such as expanding the app ecosystem the consensus is that Apple has delivered a compelling product that enhances how we interact with technology.
Conclusion
After an in-depth exploration of the Apple Vision Pro it’s clear that these smart glasses are a leap forward in augmented reality wearables. The Apple Vision Pro review highlights its cutting-edge smart glasses technology seamlessly integrating with our daily lives. The innovations in AR glasses have been redefined by Apple’s smart eyewear offering users an unparalleled experience. Don’t miss out on the opportunity to elevate your tech wardrobe; experience the future of augmented reality by getting your hands on the Apple Vision Pro today.
Technology
The Age of Generative Photography in Art: Transforming Pixels into Masterpieces
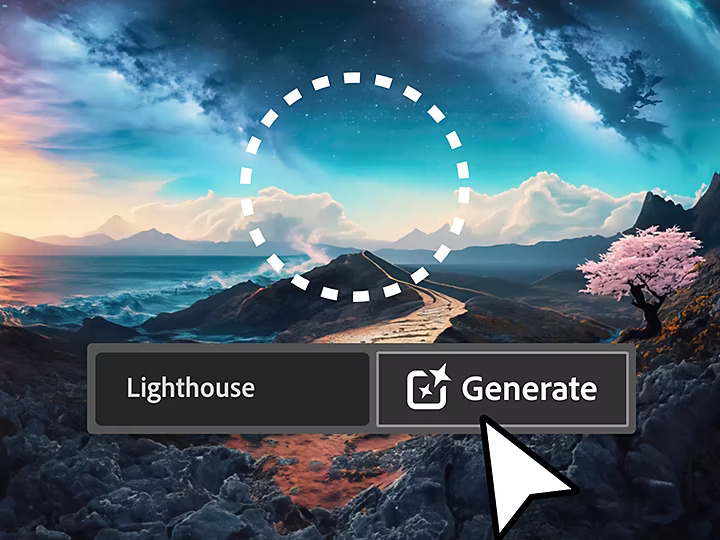
In an era where technology continually pushes the boundaries of human creativity, the art world has embraced a groundbreaking transformation: Generative Photography. This fusion of art and artificial intelligence has given rise to a new form of artistic expression, enabling artists to harness the power of algorithms and machine learning to create breathtaking visual masterpieces. In this blog post, we’ll delve into the age of Generative Photography in art, uncovering its potential, applications, and how it’s reshaping the art landscape.
Understanding Generative Photography
Generative Photography is a revolutionary concept that marries the artistic vision of photographers with the computational prowess of AI. This new-age technique goes beyond conventional photography by allowing artists to generate, manipulate, and enhance images using algorithms and machine learning. It’s not about replacing the artist’s eye, but enhancing their creative potential.
The Role of AI in Generative Photography
At the heart of Generative Photography lies AI-driven algorithms, which analyze vast datasets to create realistic and imaginative visuals. These algorithms can mimic artistic styles, enhance images, and even generate entirely new compositions. With the help of deep learning, they can identify patterns, understand visual elements, and recreate them with precision.
Applications in the Art World
Generative Photography has found its place in various art forms, from traditional photography to digital art and beyond. Artists are using it to:
1. Artistic Enhancements
Generative Photography enables artists to take an existing image and apply unique artistic filters, styles, and effects. It allows for the creation of one-of-a-kind visual experiences.
2. Artistic Collaboration
Artists are now collaborating with AI systems, working together to produce stunning pieces that merge human creativity with machine precision. The results are often nothing short of extraordinary.
3. Creative Exploration
Generative Photography encourages artists to push their creative boundaries. It serves as a tool for exploration, providing endless possibilities and room for innovation.

The Impact on Artistry
Generative Photography is not just about automation but fostering creativity. It opens doors for artists to experiment and create like never before. Here are some ways it’s impacting the art world:
Unleashing Creativity
Artists are no longer limited by the constraints of traditional photography. With AI as their ally, they can freely explore their imagination, adding unique dimensions to their work.
Breaking Boundaries
Generative Photography challenges the conventional notions of art, pushing the limits of what’s possible. It encourages artists to step outside their comfort zones and create art that surprises and captivates.
Preservation and Evolution
The combination of AI and artistry ensures that traditional and digital art forms are preserved while continually evolving. It’s an exciting era where the past meets the future.
The Future of Art
Generative Photography is still in its infancy, and its potential is boundless. As technology advances and AI becomes more sophisticated, we can expect to see even more groundbreaking developments in the art world.
Art for All
Generative Photography has the power to make art more accessible to the masses. As AI-driven art tools become user-friendly, anyone can explore their artistic side and create stunning visuals.
The Marriage of Tech and Tradition
This revolutionary technique harmonizes technology and tradition, bridging the gap between generations of artists. It’s a testament to the ever-evolving nature of art.
Embracing Change
In an age where change is constant, Generative Photography offers artists a way to adapt, innovate, and thrive in the evolving landscape of art.
Conclusion
Generative Photography is a game-changer in the world of art. It combines the artist’s vision with AI’s computational might to unlock uncharted creative possibilities. This transformative approach not only enhances traditional art but also ushers in a new era of digital artistry. As we move forward, it will be fascinating to witness the art world’s continued evolution through the lens of Generative Photography.
-
Gaming3 years ago
Download Grand Theft Auto V Reloaded (Ultimate Repack)
-
Gaming4 years ago
Make Custom Fortnite Skin in 6 easy steps
-
Cryptocurrency4 years ago
Are Bitcoin Transactions Anonymous? Everything Explained
-
Technology4 years ago
How to Stop Discord From Opening On Startup – Full Guide
-
Gaming4 years ago
Top 7 Games You Can Play With Intel HD 5500, 8GB of RAM, and an Intel i5 Processor
-
Technology3 years ago
What Is Quickbooks Online – Top Benefits of the Software Package
-
Technology3 years ago
Email Archiving Open Source – What You Must Learn
-
Cryptocurrency4 years ago
What is The Name of the General Ledger that Tracks all Bitcoin Transactions?



















Pingback: Behind the Curtains of Facial Recognition Technology